
Although the BizTalk Server was first introduced more than 20 years ago, we are still observing that it is a significant player in the Integration sector in the current Cloud era. From the new BizTalk360 enrolment, we can see that the BizTalk Server continues to impact the Integration domain.
Among the products under the Kovai.co umbrella, BizTalk360 remains a flagship offering. In summary, BizTalk360 is a single-page application (SPA) intended for Microsoft BizTalk administration and monitoring.
A minimum access policy limits a user’s access to privileged resources and permissions to the absolute minimum required to carry out an approved activity. Properly configured user permissions will guard against unwanted access and guarantee that only authorized individuals can view sensitive data.
The minimal permissions will vary depending on the organization’s policies. However, to fully utilize BizTalk360, a set of permissions is needed. Although we have documentation, we considered offering organizations a minimal number of permissions (for installation, upgrading, and management). This blog, like BizTalk360, might serve as a single point of reference for BizTalk360 with reasons.
Please be patient with me while I explain the elevated permissions and their justifications in this blog post.
Standard tools such as the BizTalk Administration Console are not intended for use in operational or support tasks. Many essential features, such as granular user access control and the ability to maintain an audit trail of support staff actions, are absent. In many instances, the default BizTalk admin console is simply too strong to entrust to unskilled or non-BizTalk personnel.
The other difficulty is in BizTalk monitoring; after deploying your solutions into a live environment, you must monitor their performance. You must be informed, for instance, when a host or receive location goes down. Customers of BizTalk are now dependent on third-party products such as HP Operations Manager, System Centre Operations Manager (SCOM), and others.
The difficult part comes when your BizTalk apps start to develop, and you must deal with the continuing alert management and SCOM setup. For the previous ten years, BizTalk360 has recognized and resolved most of the BizTalk Server integration challenges that different clients have encountered.

You frequently do not require administrator rights to install the bundled *.msi file. You may take advantage of the permission by running a simple batch script or adding the user account to certain groups. Let us glance at the BizTalk360 once everything is established during installation.
Let us split up the components and their minimum permissions.
It is possible to utilize a package distribution system with elevated rights to launch an MSI file as a non-administrator. Users can run with temporary “elevated rights” while using MSI files. This implies that consumers can install promoted MSI files. For the period of the installation, the MSI will have higher rights.
However, in the present, that is a security breach, correct? After consulting several papers, we have concluded that administrators should execute and install MSI solely for security reasons. Since BizTalk360 is constructed similarly, it is advised to run MSI with administrator permissions.
Giving the user access to a local administrator is one of the main worries for every organization. We suggest using an administrator user to launch MSI and install the BizTalk360 program to get around. To view the BizTalk360 application and subsequent settings, you may use the Default super user account. To execute the MSI, install Windows services, and construct a website, you can use a different account, a local admin.
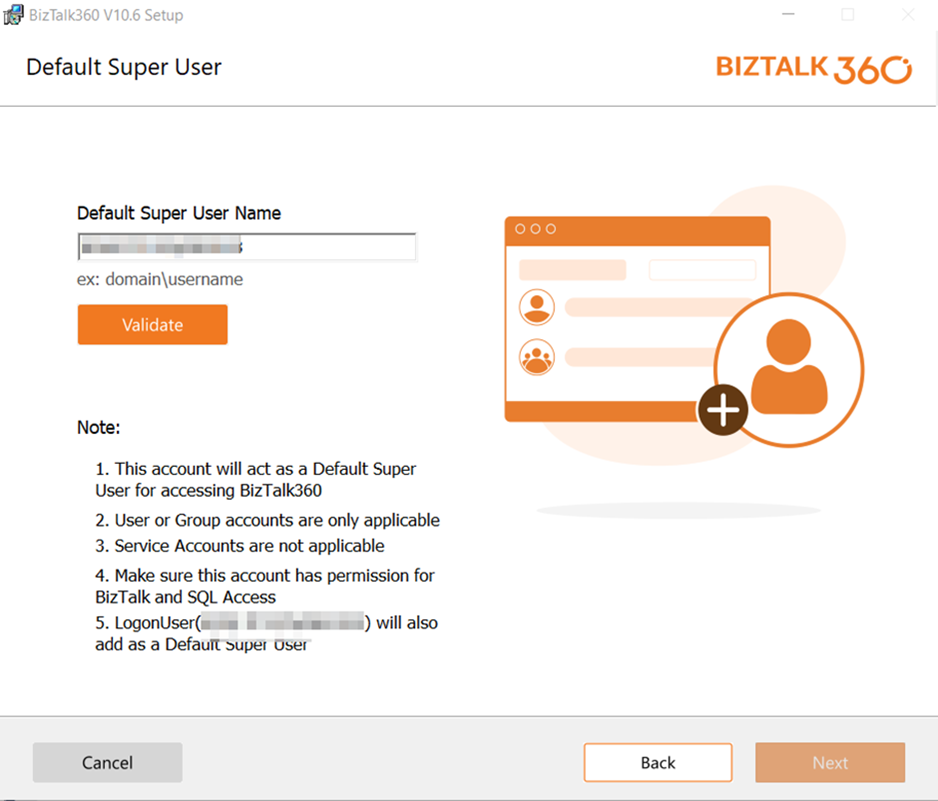
However, once more, an account must have administrator rights to install the MSI. Once the installation is complete, the service account which has the least amount of authorization can be changed.
To ensure BizTalk360’s high availability, you can deploy the BizTalk360 components on a new server using the same procedure.
The required connections may be automatically detected by the BizTalk360 MSI Installer. If any missing parts are found, you will not be able to proceed. The installation process must be stopped, the highlighted error must be fixed, and the installer must be run again if any errors are highlighted. Refer to the article to check the prerequisites.
You may use the BizTalk360 service account to create databases by treating it like any other regular account and giving it the bare minimum of permissions. It takes the “db_creator” permission to build a database. You can take it back after the installation.
After installation, the product must meet a few further requirements to function properly. Since this is the recommended way to install BizTalk360, we must ensure that the servers running BizTalk360 are configured in Windows Firewall to allow communication with the BizTalk Server, Azure, and any external services at runtime using the protocols and port number as referred to in the blog.
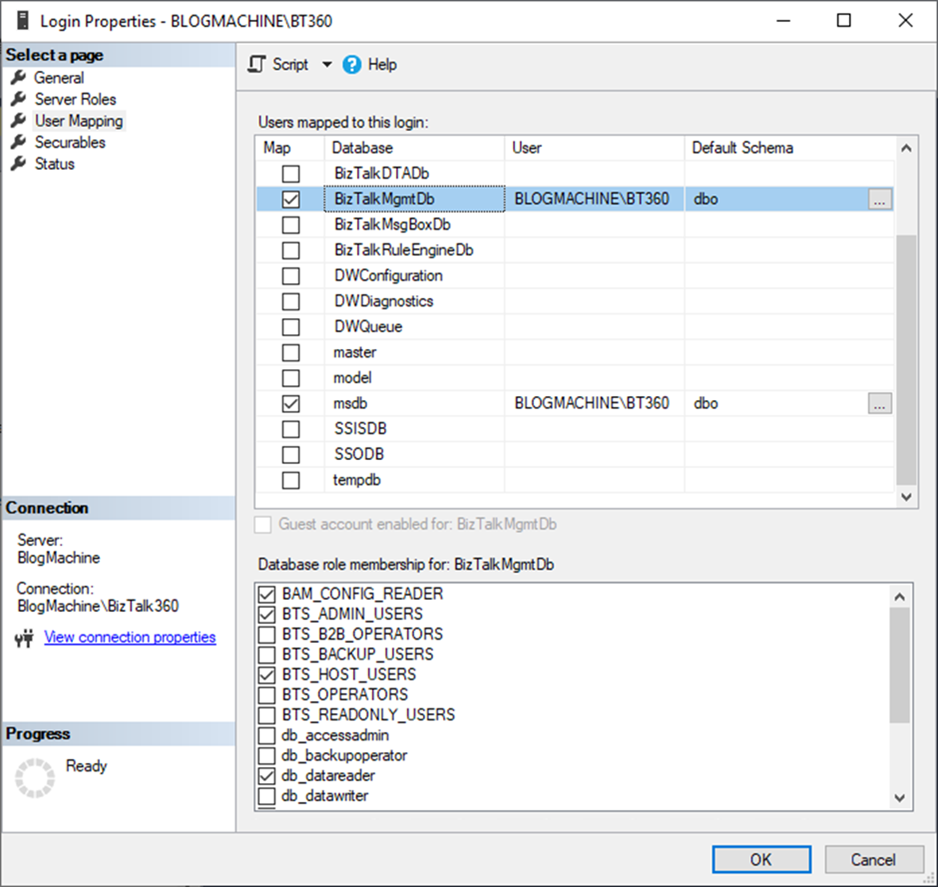
BizTalk360 abstracts all security needs; thus, people who use it will have extremely restricted access, even if they do not belong to any BizTalk groups. However, the service account will have exceptionally strong access. Once after the successful installation, the service account user will be a “db_owner” for the BizTalk360 database. Since the BizTalk360 will communicate with other BizTalk-related databases like BizTalkMgmtDb, BizTalkMsgBoxDb, BizTalkDTADb, BAM (Business Activity Monitoring), ESB, etc. you need some elevated permissions to access.
For the service account – BTS_ADMIN_USERS, BTS_HOST_USERS, BAM_CONFIG_READER, and db_datareader permissions are needed. By adding to the role, the permissions will be covered for the BizTalk-related databases modules like Applications, Message Box queries, BAM, ESB portal, EDI, Business rule composer, etc,
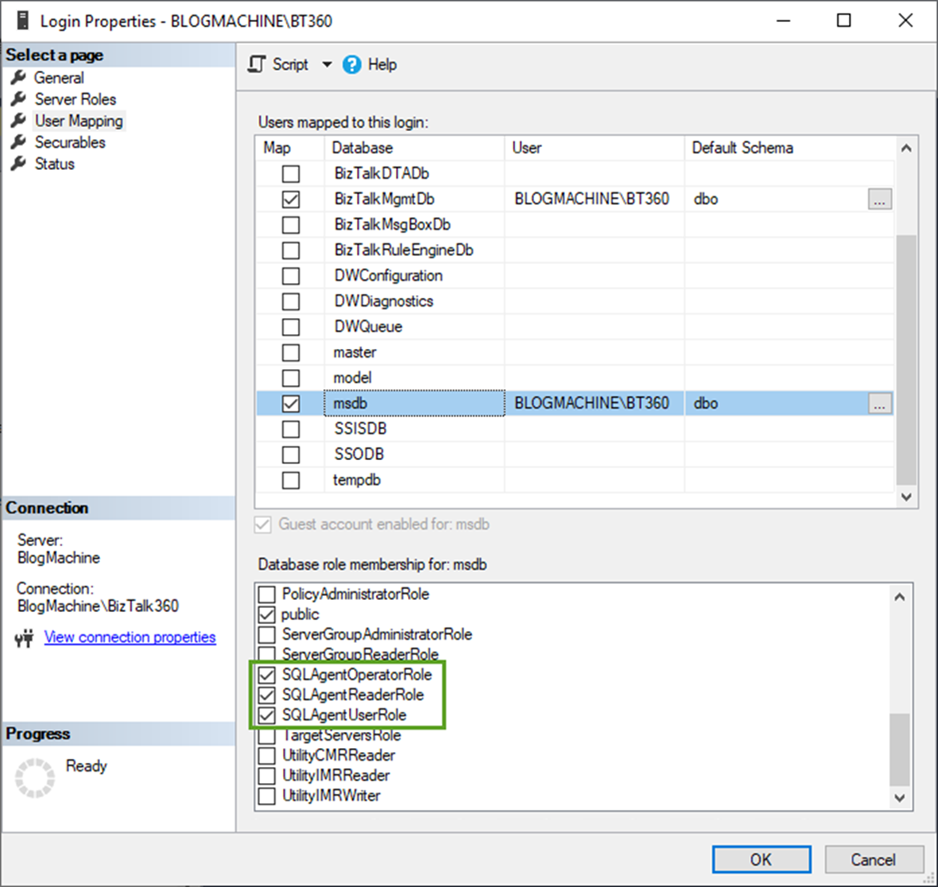
For the msdb, SQLAgentOperatorRole is necessary to access other databases and to monitor/perform actions like SQL jobs.
BizTalk360 has multiple functionalities in the Administration section related to managing the infrastructure like NT service, SQL Jobs, Host Instances, App pool, Web sites, etc., which you can perform actions like Start/Stop/Restart apart from viewing within the page.
Special permissions are usually needed to access Windows NT services to effectively manage them. The minimal set of authorizations needed are as follows:
Permissions to the administrator: To engage with services, users must have permission to administer the local system. Because they can start, stop, configure, and manage services, administrators have complete control over them.
Access control lists (ACLs): those that provide users or groups with access to a service are a means of achieving more precise control over access to certain services. Group Policy can be used to configure these rights or the Service Control Manager.
Permissions conferred by security policies: To communicate remotely with services or carry out tasks on services, users may require extra permissions from security policies.
Recall that changing services or their configurations might affect the system’s stability and security, thus providing these rights should only be done sparingly and to people you can trust.
From the experience of the BizTalk Server and BizTalk360’s infrastructure, neither will not be installed nor configured on a single machine. In most cases for high availability, it will be set up in multiple servers. Hence, it is impossible to provide permissions for the service-specific or the policies.
Hence Administrative permissions are necessary to access all the servers (like BizTalk and SQL Servers) and to avoid the complexities.

Matrix to find the built-in permissions that can be provided to the BizTalk360 service account.
| Components | Permissions |
| Active Directory permissions |
|
| At server level |
|
| BizTalkMgmtDb, BizTalkMsgBoxDb, BizTalkDTADb, BAM, ESB, SSODB, BizTalkRuleEngineDb |
|
| BizTalk360 |
|
| msdb |
|
| SELECT permission for BTS_ADMIN_USERS in BizTalkMgmtDb |
|
This is where BAM stands out; the person logging into BizTalk360 must have authorization to access BAM views in the UI (User Interface). Since not all users—including the service account—may require access to every view, this is for the most granular degree of security. Therefore, the following command must be used to provide people access to the appropriate views to which they require permission.
bm add-account -AccountName:<account name> -View:<view name>
To facilitate hybrid scenarios, BizTalk360 has capabilities that enable Azure Serverless technologies and prohibit users from abruptly moving between the Azure portal and BizTalk360.
Let us take a closer look at the BizTalk360 features for supporting Azure Serverless Administration
Matrix to find the built-in permissions that can be provided to an Azure subscription to manage the Azure resources in the BizTalk360 Application.
| Azure Resources | Built-in Permissions Available on Azure |
| Service Bus |
|
| Logic Apps |
|
| Integration Account |
|
| API Apps |
|
Find the Permissions that can be given at Azure Subscription level and actions that we can perform in BizTalk360 Application using such subscription.
1. Logic Apps:
| Azure Permissions at Subscription Level | Actions That Can be Performed on the BizTalk360 Application |
| Logic App Operator | View Logic Apps.
View the Properties of Logic Apps. |
| Logic App Contributor | View Logic Apps.
View the Properties of Logic Apps. Enable Logic App. Disable Logic App. Run trigger. Delete a Logic App. |
2. Integration Accounts:
Built In Permissions for Integration accounts such as Integration service environment contributors and Integration Service Environment developers are not required to access Integration Accounts in the BizTalk360 application.
| Azure Permissions at Subscription Level | Actions That Can be Performed on BizTalk360 Application |
| Logic App Operator | View Schemas and their properties.
View Maps and their properties. View Certificates and their properties. View Partners and its properties. View Agreements and their properties. |
3. Azure Service Bus:
|
Azure Permissions at Subscription Level |
Actions That Can be Performed on BizTalk360 Application |
| Reader – Must be provided at the Resource Group Level | |
| Azure Service Bus Data Owner – Subscription & Namespace Level. |
Lists the Queues. Lists the Topics and its Subscriptions. Queues and Topics can be Enabled. Queues and Topics can be Disabled. Queues and Topics can be Send Disabled. Queues and Topics can be Receive Disabled. Sends and Receives Messages. |
| Azure Service Bus Data Sender- Subscription & Namespace Level. |
Lists the Queues. Lists the Topics and its Subscriptions. Sends Messages. |
| Azure Service Bus Data Receiver- Subscription & Namespace Level. | Lists the Queues.
Lists the Topics and its Subscriptions. Receives Messages. |
Since we have provided the highest permissions to the service account, we are not considering other minimum permissions for features like Event Viewer, Performance Queries, and more features since they will be covered with local admin permission. Hence, we are moving to the next major part.
Direct access to SQL Server databases is not required for end users. Since the queries will be run inside the context of the service account, ‘db_datareader’ access is needed for the service account.
Unlike Microsoft SCOM and other monitoring systems, BizTalk360 is more than simply a monitoring solution. As an all-in-one operational tool for the BizTalk server (including monitoring), BizTalk360 is an excellent choice if your company does not use SCOM or any other monitoring tools, is having trouble setting up SCOM, or just wants to make the challenges associated with BizTalk server monitoring easier.
The article provides an overview of the extensive collection of artifacts that BizTalk360 monitors.
All the data will be collected and performed actions via the Service account user. As we have already provided the highest level (administrative) of permission for the BizTalk360 service account user, we do not need to provide any more permissions. But it is always important to check If the service account has access to check for the installed folder location of BizTalk360 and other required folder locations like BHM, BizTalk, SQL etc.
With the least amount of work and for the greatest possible return, the BizTalk360 analytics module will provide deeper insights into your BizTalk environment with analytical representation.
Users of BizTalk360 can activate performance data collection for Windows, SQL, IIS, and BizTalk, among other server types. Data on performance for each counter of the chosen kind will be gathered by the BizTalk360 Analytics service. By using the Manage Metrics option, users may improve the gathering of performance data. It can gather the metrics from the Windows perfmon.exe program due to the prior enhanced permissions.
Apart from the admin permission, we need to enable Default pipeline-level tracking for send and receive ports to populate data in Analytics. Please find the link to the article.
Before upgrading, make sure the services are running smoothly. You can check the service’s health by restarting them. Also, you can enter the username and password once again before updating. If it is running smoothly, upgrade to the latest version after taking a backup of the database for the safer side.
It is always healthy to be in the latest version, and BizTalk360 does not cost for an upgrade.
You can check this blog to avoid the fear of upgrading!
We are aware of the concern that giving service accounts like Local Admin and System Admin the maximum degree of access can cause security concerns. Therefore, to isolate the credentials, we advise establishing a new account for the BizTalk360 service and granting the required rights.
To limit our usage of the services, you might disable the user’s “login authorization.”
We hope the above blog gives you an insight into providing the permission and its necessary.
Using BizTalk360 facilitates improved operations, data-driven decision-making, problem detection, and resolution before they become serious and seamless operations. Its robust capabilities and ease of use are just what enterprises need to enhance their monitoring and performance.
We also provide a free trial and book a demo so you can get started right away if you are new to BizTalk360!
Happy monitoring with BizTalk360!